The No-Cloning Theorem: Why You Can't Copy-Paste Quantum Information
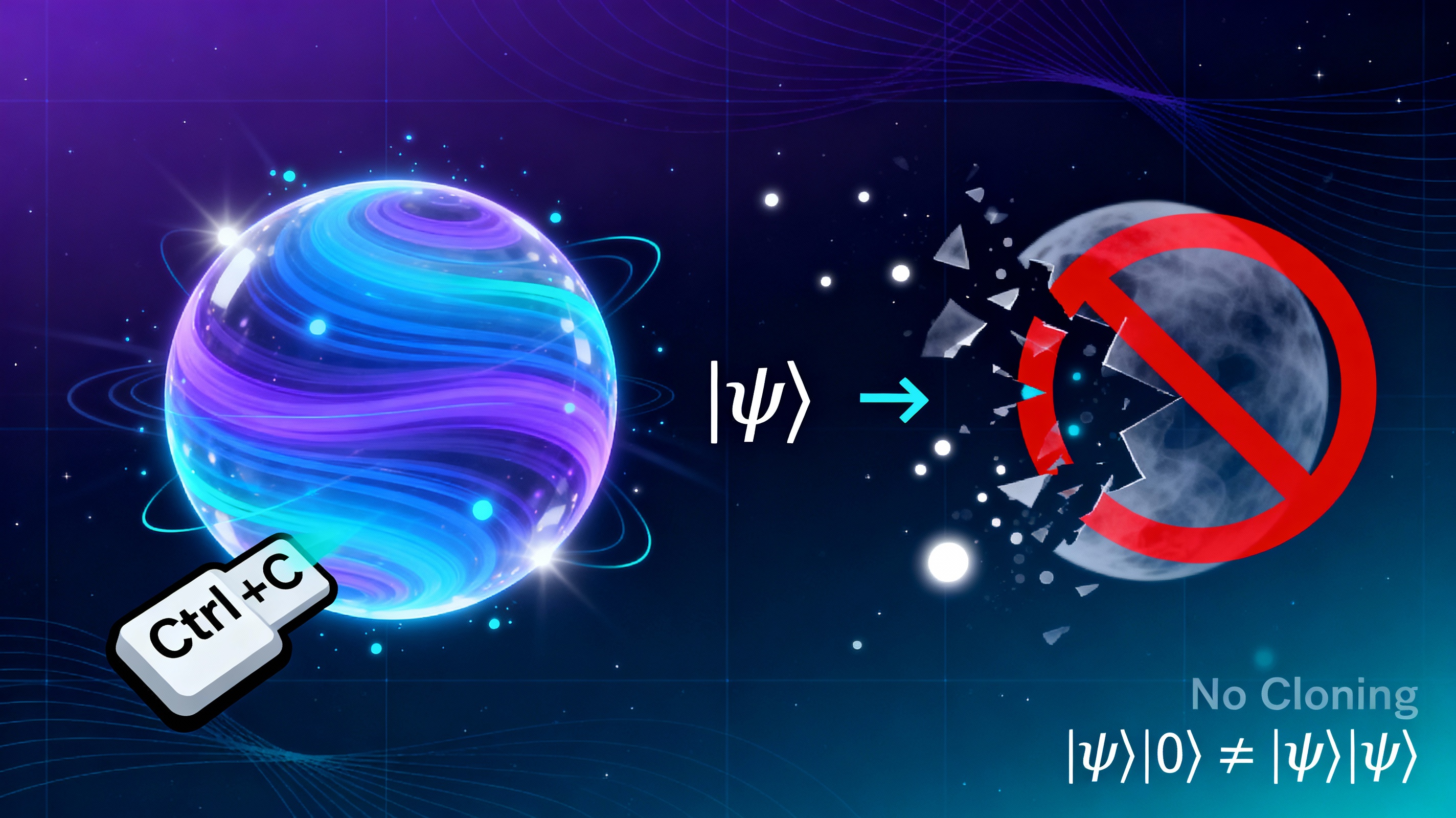
In classical computing, copying is trivial. Hit Ctrl+C, Ctrl+V, and you’ve duplicated your data perfectly. Want a backup? Copy it. Want to share a file? Copy it. Want to debug? Copy the state and inspect it without disturbing the original.
In quantum computing? Nature says no.
The no-cloning theorem is one of the most surprising and fundamental constraints in quantum mechanics. It states, mathematically and definitively, that you cannot create an identical copy of an arbitrary unknown quantum state.
Not “it’s hard to copy.” Not “we haven’t figured out how yet.” It’s impossible. Period.
Today, we’ll explore why this limitation exists, what it means for quantum computing, and how this apparent weakness becomes quantum cryptography’s greatest strength.
(As beautifully explained in Andrew Thomas’s Hidden In Plain Sight 10, this isn’t just a theoretical curiosity—it’s a fundamental feature of quantum reality.)
The Setup: Why Would We Want to Clone Quantum States?
Before we understand why cloning is impossible, let’s understand why we’d want it:
In classical computing, copying enables:
- Backups: Store redundant copies in case of errors
- Distribution: Share information without losing your original
- Parallel processing: Run multiple computations on the same data
- Debugging: Inspect program state without disrupting execution
- Error correction: Compare copies to detect and fix errors
Quantum computing would benefit enormously from these capabilities. Imagine being able to:
- Copy a qubit’s superposition state for backup
- Duplicate a quantum computation’s intermediate results
- Make perfect copies of an unknown quantum state for analysis
This would make quantum computers vastly more practical. So why can’t we do it?
The No-Cloning Theorem: The Mathematical Proof
The no-cloning theorem was proven independently by William Wootters and Wojciech Zurek, and by Dennis Dieks in 1982. Here’s the essence of their argument, stripped to its core logic:
The Claim: There is no quantum operation that can take an arbitrary unknown quantum state |ψ⟩ and produce two identical copies of it.
(Quick refresher: |ψ⟩ is quantum notation for a quantum state, and |0⟩ and |1⟩ represent the two basis states of a qubit. If this notation is unfamiliar, check out our previous post on superposition for a full explanation.)
The Proof (Simplified):
Suppose we have a “cloning machine” that works as follows:
- Input: One qubit in state
|ψ⟩and one blank qubit in state|0⟩ - Output: Two qubits, both in state
|ψ⟩
Mathematically, this would be: |ψ⟩|0⟩ → |ψ⟩|ψ⟩
Let’s test this with two different quantum states:
Start with |0⟩:
|0⟩|0⟩ → |0⟩|0⟩ ✓ (This should work)
Start with |1⟩:
|1⟩|0⟩ → |1⟩|1⟩ ✓ (This should also work)
So far, so good. But quantum mechanics is linear—it preserves superpositions. This means any valid quantum operation must work consistently when applied to a superposition of states, not just individual basis states.
So if our cloning machine works for |0⟩ and |1⟩, it must also work for their superposition:
Start with (|0⟩ + |1⟩)/√2 (an equal superposition—if you need a refresher on what superposition means and why it’s not just a probability, see our earlier post):
By linearity, the cloning machine must do:
[(|0⟩ + |1⟩)/√2]|0⟩ → ?
First, let’s distribute the input state to see what we’re starting with:
[(|0⟩ + |1⟩)/√2]|0⟩ = (1/√2)[|0⟩|0⟩ + |1⟩|0⟩]
Now, if we apply the cloning operation linearly (using the rules we established for |0⟩ and |1⟩):
(1/√2)[|0⟩|0⟩ + |1⟩|0⟩] → (1/√2)[|0⟩|0⟩ + |1⟩|1⟩]
But this is not what we wanted! We wanted:
[(|0⟩ + |1⟩)/√2][(|0⟩ + |1⟩)/√2] = (1/2)[|0⟩|0⟩ + |0⟩|1⟩ + |1⟩|0⟩ + |1⟩|1⟩]
These are different quantum states. The cloning machine produces the wrong result for superposition states.
The Inescapable Conclusion:
A universal quantum cloning machine—one that works for any arbitrary quantum state—cannot exist. The linearity of quantum mechanics forbids it.
What Does “No Cloning” Actually Mean?
Let’s be precise about what the theorem does and doesn’t say:
What you CAN’T do:
- Copy an arbitrary unknown quantum state perfectly
- Create a universal cloning machine that works for all quantum states
- Make a backup of a quantum state without destroying the original
What you CAN do:
- Copy classical information (measured results) as much as you want
- Copy a known quantum state (e.g., always prepare qubits in
|0⟩) - Create imperfect copies that are “close” to the original but not exact
- Make copies if you know the state belongs to a specific set (orthogonal states—states that are perfectly distinguishable from each other, like
|0⟩and|1⟩)
The key word is arbitrary. If you already know what state you’re trying to copy (e.g., you know it’s |0⟩ or |1⟩), you can just prepare a new qubit in that same state. The problem arises when you don’t know the state and want to copy it anyway.
Why Does This Matter? The Practical Implications
The no-cloning theorem has profound consequences:
1. No Perfect Quantum Backups
In classical computing, you can save your program’s state, try something, and restore if it fails. In quantum computing, once you’ve created a quantum state, you can’t make a perfect copy for safekeeping. If your quantum computation fails, you can’t just restore from backup—you have to start over.
2. Quantum Debugging is Nearly Impossible
Want to know what’s happening inside your quantum algorithm? Tough luck. You can’t copy the intermediate state to inspect it without destroying the original computation. Measuring it collapses the superposition (as we explored in our post on the double-slit experiment), and you can’t make a copy to measure instead.
This is why quantum debugging is so challenging—you’re flying blind through the computation.
3. No “Quantum Xerox Attacks”
Here’s where things get interesting. Suppose you intercept a quantum cryptographic key being transmitted. You’d love to copy it, send the copy along (so nobody knows you intercepted it), and keep the original to decrypt messages later.
No-cloning says: nope.
If you try to measure the quantum state to copy it, you’ll collapse its superposition and introduce detectable errors. The legitimate parties will know someone tampered with the key.
This is the foundation of Quantum Key Distribution (QKD)—provably secure cryptography based on the laws of physics, not mathematical assumptions.
4. No Quantum Superluminal Communication
Without no-cloning, you might imagine faster-than-light communication schemes: entangle two particles (create a quantum correlation between them), separate them by light-years, manipulate one, clone the other to extract information instantly.
No-cloning (along with the no-communication theorem—which states that quantum entanglement cannot transmit information faster than light) blocks this. The universe protects causality.
(We’ll explore entanglement in detail in an upcoming post, but for now: think of it as a special quantum correlation where measuring one particle instantly affects the other, no matter the distance.)
Real-World Example: BB84 Quantum Cryptography
Let’s see no-cloning in action with the BB84 quantum key distribution protocol (named after Bennett and Brassard, 1984):
The Setup:
- Alice wants to send Bob a secret key
- They use qubits to encode bits of the key
- Eve (an eavesdropper) tries to intercept and copy the qubits
The Protocol:
- Alice prepares qubits in one of four possible states (two bases: rectilinear
|0⟩, |1⟩and diagonal|+⟩, |−⟩) - She sends them to Bob through a quantum channel (a communication path that preserves quantum states, like a fiber optic cable)
- Bob randomly chooses a measurement basis for each qubit (rectilinear or diagonal—like choosing which angle to view the qubit from)
- Alice and Bob publicly compare their chosen bases (not the results!)
- They keep only the bits where they used the same basis
Where No-Cloning Protects Them:
If Eve tries to intercept:
- She doesn’t know which basis Alice used for each qubit
- She can’t clone the qubit to measure it in both bases
- Whatever basis she chooses, she has a 50% chance of being wrong
- When she’s wrong, she disturbs the qubit’s state
- Bob receives corrupted qubits, and the error rate spikes
- Alice and Bob detect Eve’s presence and abort
The key insight: Without no-cloning, Eve could make perfect copies, measure them in all bases, and relay perfect qubits to Bob. No-cloning makes eavesdropping detectable.
This isn’t cryptography based on “it’s too hard to break”—it’s cryptography based on “the laws of physics forbid it.”
But What About Quantum Error Correction?
Wait a minute. If you can’t copy quantum states, how do quantum computers do error correction? Classical error correction relies on making redundant copies and comparing them.
Great question! Quantum error correction is possible, but it’s far more subtle:
Classical error correction:
- Copy bit: 0 → 000
- If one flips: 001 or 010 or 100
- Majority vote reveals the error
Quantum error correction:
- Can’t copy the state:
|ψ⟩ ≠ |ψ⟩|ψ⟩|ψ⟩ - Instead, use entanglement (quantum correlations between qubits) to spread quantum information across multiple qubits
- Encode one logical qubit into multiple physical qubits
- Measure error syndromes (observable patterns that indicate errors occurred, like checking parity, without revealing the actual quantum state) without measuring the quantum state itself
- Correct errors based on syndrome measurements
This works because:
- We’re not cloning arbitrary states
- We’re creating a specific entangled state that encodes the information redundantly
- We’re measuring properties of the encoding, not the quantum state itself
No-cloning is preserved—we never create independent copies of the quantum state. We create a single, more complex quantum state that’s resilient to errors.
(We’ll dive deep into quantum error correction in a later post—it’s one of the most ingenious workarounds in quantum computing.)
The Philosophical Angle: Information is Physical
The no-cloning theorem reveals something profound: quantum information is fundamentally different from classical information.
Classical information is abstract—you can copy a pattern of bits without limit. It’s the pattern that matters, not the physical substrate.
Quantum information is tied to the physical state of the system. You can’t separate the information from the quantum state itself. The state is the information.
This connects to a deeper principle in physics: information is physical. It’s not an abstract mathematical concept floating above reality—it’s embedded in the physical laws that govern our universe.
(Philosophical aside: This resonates with certain Vedantic ideas about knowledge and reality. In Advaita Vedanta, knowledge (jñāna) is not separate from the knower or the known—they form a non-dual unity. Similarly, quantum information cannot be separated from the quantum state. The information, the state, and the measurement are aspects of one unified reality. We’ll explore these parallels in our philosophical reflection posts.)
Can We Ever Bend the No-Cloning Theorem?
While perfect cloning is impossible, physicists have found interesting workarounds:
1. Quantum Teleportation
You can “move” a quantum state from one location to another without physically transporting the particle:
- Uses entanglement (quantum correlation between particles) + classical communication (regular information transmission)
- The original state is destroyed in the process (so no cloning!)
- The state reappears elsewhere
This is like “cut and paste” instead of “copy and paste.”
(We’ll cover quantum teleportation in detail in a future post—it’s one of the most mind-bending protocols in quantum computing.)
2. Probabilistic Cloning
You can create imperfect copies with probability less than 100%:
- Make clones that are “close enough” to the original
- Success probability depends on how different the possible states are
- Useful in some quantum protocols, but not a substitute for perfect cloning
3. Cloning Known Subsets
If you know the state is one of a small set of orthogonal states (e.g., |0⟩ or |1⟩), you can effectively clone by measuring and re-preparing:
- Measure to determine which state it is
- Prepare multiple qubits in that state
- This works because orthogonal states are distinguishable
But for arbitrary superpositions? No luck.
The Bottom Line: A Limitation That’s Actually a Feature
The no-cloning theorem seems like a major inconvenience. And in many ways, it is—quantum debugging, error correction, and backups are all significantly harder because of it.
But this “limitation” is also a superpower:
- It makes quantum cryptography provably secure
- It protects causality and prevents paradoxes
- It reveals the unique nature of quantum information
- It forces us to think differently about computation and information
In the quantum world, copying isn’t just hard—it’s forbidden by the fundamental laws of nature. And that makes quantum information special, powerful, and impossible to forge.
What’s Next?
Now that you understand why quantum states can’t be copied, you’re ready to explore how we actually manipulate them through quantum gates.
Next up: Single-Qubit Gates—the Hadamard, Pauli, Phase, and rotation gates that transform quantum states on the Bloch sphere.
How do you create superposition? Flip qubits? Change phase? And why are these gates represented as rotations in 3D space?
That’s coming soon. But here’s a teaser: every single-qubit operation is just a rotation on the Bloch sphere. Quantum computing is geometry in disguise.
Stay curious. 🌊
References and Further Reading
Original Papers
- Wootters, W. K., & Zurek, W. H. (1982). “A single quantum cannot be cloned.” Nature, 299(5886), 802-803. https://doi.org/10.1038/299802a0
- The foundational paper proving the impossibility of universal quantum cloning
- Dieks, D. (1982). “Communication by EPR devices.” Physics Letters A, 92(6), 271-272. https://doi.org/10.1016/0375-9601(82)90084-6
- Independent proof of the no-cloning theorem published the same year
- Bennett, C. H., & Brassard, G. (1984). “Quantum cryptography: Public key distribution and coin tossing.” Proceedings of IEEE International Conference on Computers, Systems and Signal Processing, 175-179.
- The original BB84 quantum key distribution protocol
Books and Learning Resources
-
Hands-On: Hidden In Plain Sight 10: How To Program A Quantum Computer by Andrew H. Thomas—Excellent discussion of no-cloning and its implications for quantum computing
-
Nielsen, M. A., & Chuang, I. L. (2010). Quantum Computation and Quantum Information (10th Anniversary Edition). Cambridge University Press.
- The definitive textbook; see Chapter 12 for detailed treatment of quantum information theory
Interactive Tools
- IBM Quantum Composer: Try quantum teleportation experiments hands-on at https://quantum-computing.ibm.com/composer
- Qiskit Textbook: Free quantum computing tutorials at https://qiskit.org/learn
Previous Post: Superposition Explained: Why Qubits Aren’t Just Fancy Coins
Next Post: Single-Qubit Gates: Rotations on the Bloch Sphere (Coming soon)
📢 Stay Updated: Follow ProbableQ on LinkedIn for more quantum computing insights and updates on this blog series!
Have questions or insights? Connect with me on LinkedIn or Twitter.